top stories

News
Vermont Reports Its First Case of the Measles Since 2018
Photo 146292007 © Felipe Caparros Cruz | Dreamstime.com

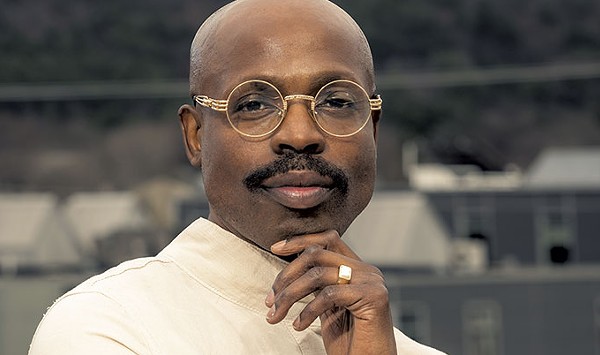
Theater
Waitsfield’s Shaina Taub Arrives on Broadway, Starring in Her Own Musical, ‘Suffs’
Courtesy Of Shervin Lainez / Mary Ann Lickteig

Food + Drink Features
New Sheep Shop Café on a South Woodbury Homestead Gathers the Herd
Jordan Barry ©️ seven Days

Housing Crisis
Barre to Sell Two Parking Lots for $1 to Housing Developer
Anne Wallace Allen ©️ seven Days





















































find, follow, fan us: